- Forums
- Knowledge Base
- Customer Service
- FortiGate
- FortiClient
- FortiAP
- FortiAnalyzer
- FortiADC
- FortiAuthenticator
- FortiBridge
- FortiCache
- FortiCarrier
- FortiCASB
- FortiConnect
- FortiConverter
- FortiCNP
- FortiDAST
- FortiDDoS
- FortiDB
- FortiDNS
- FortiDeceptor
- FortiDevSec
- FortiDirector
- FortiEDR
- FortiExtender
- FortiGate Cloud
- FortiGuard
- FortiHypervisor
- FortiInsight
- FortiIsolator
- FortiMail
- FortiManager
- FortiMonitor
- FortiNAC
- FortiNAC-F
- FortiNDR (on-premise)
- FortiNDRCloud
- FortiPAM
- FortiPortal
- FortiProxy
- FortiRecon
- FortiRecorder
- FortiSandbox
- FortiSASE
- FortiScan
- FortiSIEM
- FortiSOAR
- FortiSwitch
- FortiTester
- FortiToken
- FortiVoice
- FortiWAN
- FortiWeb
- Wireless Controller
- RMA Information and Announcements
- FortiCloud Products
- ZTNA
- 4D Documents
- Customer Service
- Community Groups
- Blogs
- Fortinet Community
- Knowledge Base
- FortiGate
- Technical Tip: FortiGate WSSO SSID Authentication ...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
| Description | This article describes that WSSO SSID users fail to authenticate when using a local group with a Radius server but can authenticate directly with Radius server authentication. |
| Scope | FortiGate v6.x.x and v7.x.x. |
| Solution |
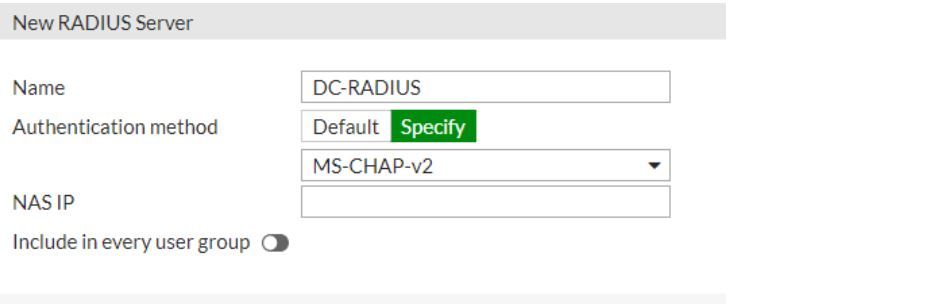
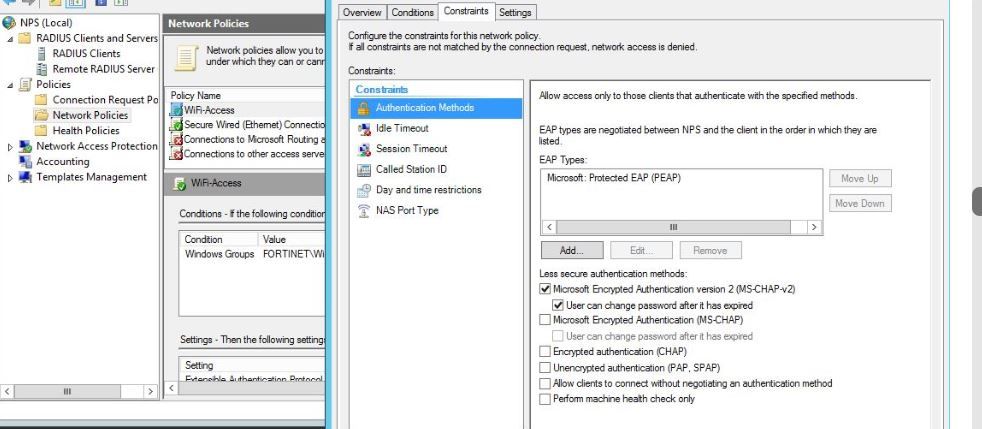
Example: FortiGate uses authentication protocol Ms-Chap-v2 to connect with the Radius server and EAP is enabled on the NPS server:
on FortiGate CLI:
diag debug app fnbamd -1 diag debug en
[587] __fnbamd_cfg_get_radius_list_by_group-Loading RADIUS server 'DC-RADIUS' for usergroup 'WiFi' (4)
In the above debugs, Fortigate still uses PAP for the Local Group even when MS-Chap-v2 is configured on the Radius server settings. Due to this users are unable to authenticate.
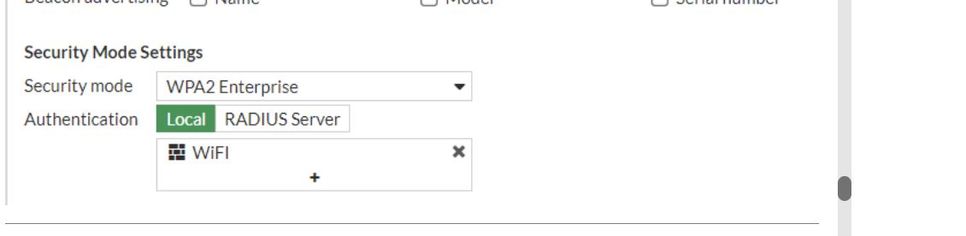
FortiGate does not force the authentication protocol for SSID authentication. PEAP authentication needs to be enabled on the end devices. If the end user is a Windows PC, it is necessary to enable EAP-MSCHAP-v2 in the wireless network security of the PC.
Related article: Configuring WiFi with WSSO using Windows NPS and user groups |
The Fortinet Security Fabric brings together the concepts of convergence and consolidation to provide comprehensive cybersecurity protection for all users, devices, and applications and across all network edges.
Copyright 2024 Fortinet, Inc. All Rights Reserved.